Discover how red teaming services can safeguard your e-commerce business from cyber threats. Improve security, protect customer data, and boost trust.
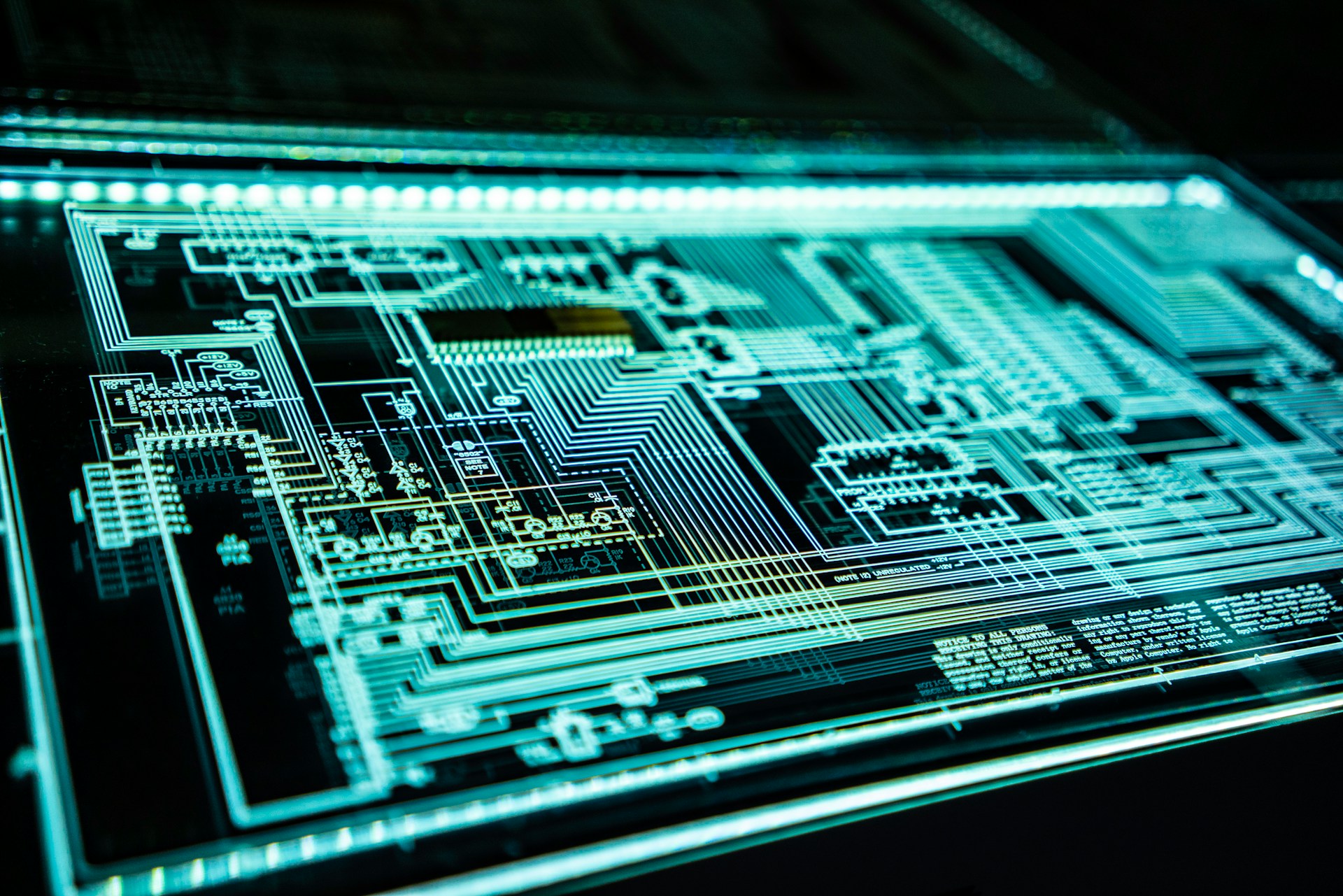
Red teaming services, as a specialized security solution, can be described as an efficient and multifaceted strategy designed to strengthen the protection of various organizations, including e-commerce ones, against emerging cyber threats. Red teaming is a complex reiteration of the general security audit. The process involves an active examination of the organization’s defenses with the help of threat scenarios imitating actual cyber-attacks. This method of security features security specialists pretending to be other adversaries to penetrate the organization’s system and see the gaps and flaws present in the security within the organization.
Understanding Red Teaming Services
When it comes to red teaming in cyber-security, red teaming refers to a detailed and preemptive examination of an organization’s security situation through the use of realistic cyber threats. It is different from other security tests like pen-testing in that it replicates the actual behaviors that the attackers are likely to employ, thereby exposing other risks that may not be seen during other tests.
In red teaming, a team of people with unique security knowledge and skills known as red tea conducts an attack on the organization’s systems, networks, and applications by emulating hackers’ operations. As such, the purpose of realistic security assessments is to validate security controls, incident response measures, and the organization’s readiness to counter cyber threats.
Red teaming entails:
- Simulated Attack Scenarios: Red teamers design and conduct attacks that are as close as possible to real-life threats that an organization may encounter, such as phishing, network compromise, or data leakage.
- Advanced Techniques: Red teaming involves using advanced methods, tools, and processes similar to those of a real-world attacker to capitalize on new avenues of attack, gain new access to the company’s network, and evolve constantly.
- Comprehensive Assessment: The red team analyses the technical solutions and personnel’s awareness, security policies, and response procedures to give general information about the security level in organizations.
- Reporting and Recommendations: As for the engagement’s outcome, the red team offers a comprehensive write-up containing observations, identified risks, and opportunities for enhancing the organization’s protection against cyber threats.
With red team engagements, organizations can recognize and learn where security weaknesses lie, confirm the efficiency of deployment security controls, and fortify their security approach to counter new cyber threats to an organization’s assets, information, and processes.
Steps to consider when implementing red teaming services in an e-commerce environment
Implementing red teaming services in an e-commerce environment requires careful planning and consideration to ensure that the exercise aligns with online retail businesses’ unique security needs and operational characteristics. Here are the essential steps to consider when implementing red teaming services in an e-commerce environment:
- Define Objectives and Scope: Clearly outline the specific objectives of the red team engagement, such as identifying vulnerabilities in e-commerce platforms, testing payment processing security, or assessing customer data protection measures.
- Engage Stakeholders: Collaborate with key stakeholders, including IT and security teams, e-commerce platform administrators, and business leaders, to gain buy-in, establish clear expectations, and ensure alignment with business objectives.
- Threat Modeling: Conduct a thorough threat modeling exercise to identify the most critical assets, potential attack vectors, and threats specific to the e-commerce environment, including customer data, payment systems, and web application security.
- Scenario Development: Develop realistic attack scenarios tailored to the e-commerce ecosystem, considering risks such as account takeover, payment fraud, supply chain attacks, and web application vulnerabilities.
- Rules of Engagement: Establish clear rules of engagement to define the boundaries of the red team exercise, including prohibited actions, systems exempt from testing, and communication protocols to avoid disrupting production environments.
- Security Controls Assessment: Evaluate the effectiveness of security controls relevant to e-commerce, such as web application firewalls, secure payment processing, data encryption, user access controls, and protection against DDoS attacks.
- Social Engineering Testing: Include simulated social engineering attempts to gauge the susceptibility of e-commerce staff to phishing, pretexting, or other forms of manipulation that could lead to security breaches.
- Incident Response Simulation: Test the e-commerce business’s incident response capabilities, including the detection, containment, and mitigation of simulated cyber-attacks, to assess the readiness to address security incidents effectively.
- Compliance Assessment: Ensure that the red team engagement aligns with relevant compliance requirements, such as PCI DSS for payment card security and GDPR for data protection, to validate adherence to industry standards.
- Post-Engagement Analysis and Improvement: Analyze the findings from the red team engagement, prioritize vulnerabilities, and implement remediation measures to enhance the security posture of the e-commerce environment. Use the results to improve security controls and practices continuously.
By following these steps, e-commerce businesses can effectively implement red teaming services to proactively identify and address security risks, fortify their defenses against cyber threats, and bolster the protection of customer data and transactions.
Conclusion
Red teaming services are a way that can assist an e-commerce business in avoiding cyber threats because they aim at finding all the risks to the company’s systems, networks, and applications. As a result, it is possible to identify weaknesses in security measures, assess protective controls, and improve the organization’s reaction to threats and incidents. Red teaming services can also discover insecurities not revealed in conventional security audits related to the company’s compliance with guidelines such as PCI DSS or GDPR. This approach also proves effective for strengthening customer data and transactions’ safeguarding, improving security measures, and maintaining constant security escalation. Finally, it should be noted that the threat of cybersecurity incidents will always be relevant, so addressing them with the help of a red team will benefit an e-commerce business and strengthen the customers’ trust in the company and its brand.
Was this news helpful?




 Yes, great stuff!
Yes, great stuff! I’m not sure
I’m not sure No, doesn’t relate
No, doesn’t relate



