
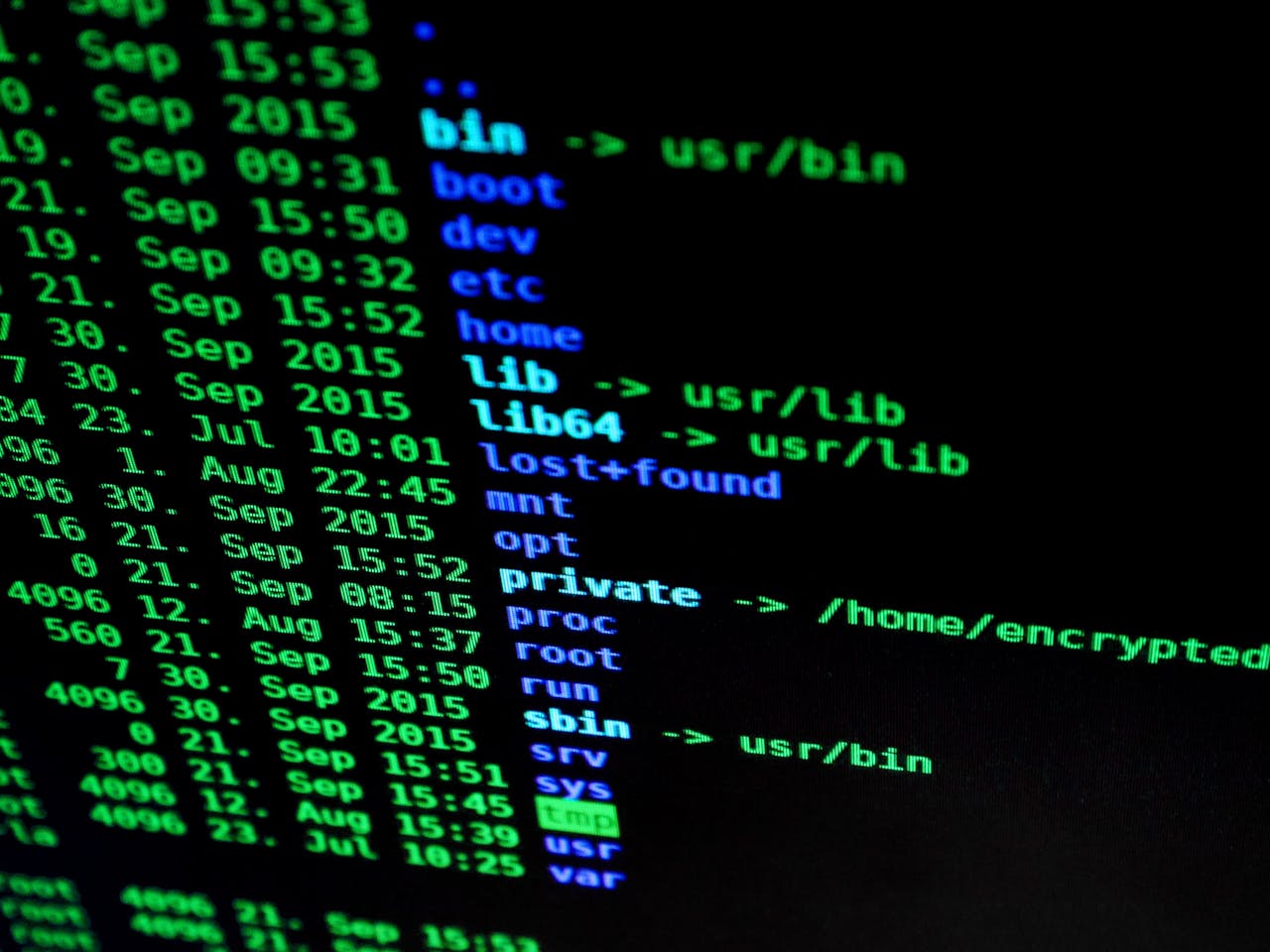
Explore cutting-edge security measures to secure your enterprise data. This overview provides insights into the latest techniques and strategies to protect your organization's valuable information from cyber threats.
Safeguarding enterprise data is more critical than ever. With cyber threats evolving at an unprecedented rate, traditional security measures are often insufficient. To adequately protect sensitive information, businesses must adopt a multi-layered approach that incorporates the latest advancements in security technology. This blog explores some of the most effective and innovative security measures available today, designed to keep your enterprise data secure from modern cyber threats.
Reliable Connectivity
Reliable connectivity is the backbone of any successful enterprise. As businesses expand globally, the need for a robust, secure, and agile network infrastructure becomes increasingly vital. This is where global managed SD-WAN (Software-Defined Wide Area Network) comes into play. By leveraging SD-WAN, businesses can connect their global branches and remote offices to a centralized, secure network. This helps ensure consistent connectivity while reducing the risk of data breaches caused by unsecured connections.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) has become a cornerstone of modern enterprise security. MFA adds an extra layer of protection by requiring users to present multiple forms of identification before accessing sensitive data or systems. Typically, these factors include something the user knows (like a password), something the user has (such as a smartphone or a security token), and something the user is (biometric verification like fingerprint or facial recognition). This multi-layered approach makes it significantly more challenging for unauthorized users to gain access, even if they manage to compromise one layer. Implementing MFA can substantially reduce the risk of breaches and unauthorized access, providing an essential boost to overall security postures.
Zero Trust Security Model
The Zero Trust Security Model is a revolutionary approach that fundamentally shifts how we think about network security. Rather than relying on outdated assumptions that entities within a network are inherently trustworthy, Zero Trust adopts a “never trust, always verify” philosophy. This model requires continuous authentication and authorization of all users and devices, regardless of their location within or outside the network perimeter.
Every access request is meticulously inspected, users are authenticated, and devices are given the least privilege needed to perform their functions. This granular level of security reduces the attack surface and limits potential damage in case of a breach. By instituting stringent verification processes and segmenting the network to isolate sensitive resources, the Zero Trust Security Model provides a robust framework to safeguard enterprise data against even the most sophisticated cyber threats.
Artificial Intelligence in Cybersecurity
Artificial Intelligence (AI) is transforming the landscape of cybersecurity by offering advanced tools to identify, mitigate, and prevent cyber threats. AI-powered systems can analyze vast amounts of data at unprecedented speeds, identifying patterns and anomalies that might be indicative of malicious activities. Machine learning algorithms can be trained on historical data to predict potential threats and automate responses to known attack vectors, drastically reducing the time between detection and action.
AI enhances threat intelligence by continuously evolving and adapting to new and emerging threats, making it particularly effective against sophisticated attacks like zero-day exploits and advanced persistent threats (APT). AI-driven cybersecurity solutions also support behavioral analytics, monitoring user behavior to detect unusual activities that could indicate a security breach. By integrating AI into their cybersecurity strategies, enterprises can significantly bolster their defense mechanisms, ensuring a more proactive and dynamic stance against the ever-changing cyber threat landscape.
Secure Access Service Edge (SASE)
Secure Access Service Edge (SASE) is an emerging framework that converges network security and wide-area networking (WAN) into a single, cloud-delivered service model. SASE integrates multiple security functions, including secure web gateways (SWG), cloud access security brokers (CASB), firewall-as-a-service (FWaaS), and zero trust network access (ZTNA), with WAN capabilities such as SD-WAN. This holistic approach simplifies the architecture, reduces complexity, and provides a more efficient way to manage and secure enterprise networks.
SASE is designed to address the challenges of modern enterprises, where a dispersed workforce and the adoption of cloud services have rendered traditional, perimeter-based security models less effective. By moving security to the cloud and closer to the users and devices that need access, SASE ensures that every connection, regardless of location, is authenticated, authorized, and encrypted. This ensures consistent security policies and improved performance, no matter where users are or which applications they are accessing.
Implementing SASE can lead to significant improvements in security posture and operational efficiency. It provides a unified solution for network and security needs, reducing the burden on IT teams and enabling faster, more agile responses to security incidents. By leveraging the cloud’s scalability and flexibility, SASE supports the dynamic needs of modern enterprises, ensuring robust protection against evolving cyber threats.
Securing enterprise data requires a comprehensive and multi-layered approach that incorporates the latest advancements in security technology. From reliable connectivity to cutting-edge solutions like AI-driven cybersecurity and SASE, businesses must continually evolve their security strategies to stay ahead of modern cyber threats. By implementing these cutting-edge security measures, enterprises can ensure their critical data remains safe from unauthorized access or malicious activities while enabling seamless collaboration and growth.
Was this news helpful?




 Yes, great stuff!
Yes, great stuff! I’m not sure
I’m not sure No, doesn’t relate
No, doesn’t relate



